Started in the USA as Cybersecurity Awareness Month and spread across the world, Cybersecurity Month reminds us that digitization has its challenges that companies in all countries need to face. But what are the challenges today? Have they changed over time? How should you avoid them, and what should you pay attention to, to make your business safe and resistant to various attacks? Let’s take a look at what we can learn in October about cybersecurity.
Challenges for Digitized Business
Ransomware
In 2024, ransomware attacks will still be one of the leading cyber threats. Unfortunately, its hazardous potential constantly grows as it gets more complex. Ransomware affects data storage in several ways, depending on the type and severity of the attack. It leads to a couple of unfortunate consequences every company wishes to avoid:
- Ransomware can alter or damage your files, making them unusable or unreliable, leading to data corruption. It can change the file extensions, modify the file headers, or insert malicious code into your files.
- Data corruption directly leads to data loss, which happens when ransomware encrypts or deletes files, making them inaccessible or unrecoverable. Even after paying the ransom, there is no guarantee that the attacker will provide the decryption key or restore your data anyhow.
- Another way ransomware may affect your business is data exposure. Stealing or leaking your files, making them available to unauthorized parties – that’s what you can expect if your data falls into the wrong hands. It violates your data privacy, confidentiality, sovereignty and may lead to the loss of a potential client’s trust.
How to avoid:
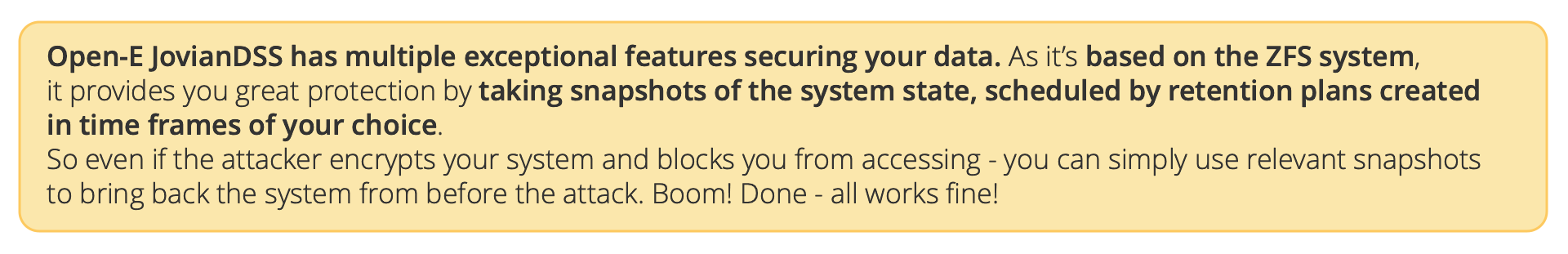
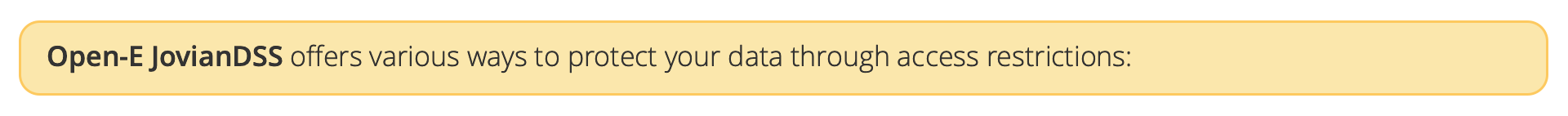
![]() Using data storage software that protects your data against corruption, encryption, or simply saves that system state from before the attack and lets you bring it back at any given moment.
Using data storage software that protects your data against corruption, encryption, or simply saves that system state from before the attack and lets you bring it back at any given moment.
Malware: Software That Harms a System
Viruses, trojan horses, and spyware are all types of malware that destroy a company’s data infrastructure. After the COVID-19 pandemic, once people returned to their offices, malware attack numbers significantly rose while decreasing in 2020/21. Nowadays, it has become one of the biggest cyber threats again. Developing cryptocurrency in recent years has contributed to situations such as hackers taking control of victims’ computers to create illegal cryptocurrencies. They may also take control of routers, cameras, and microphones, which make voyeurism and eavesdropping possible. Hackers can listen to confidential and sensitive information like passwords, etc.
How to avoid:
![]() Well-optimized and safe firewalls and antivirus software are the most commonly used. These methods lower the chances of being a victim.
Well-optimized and safe firewalls and antivirus software are the most commonly used. These methods lower the chances of being a victim.
Social Engineering Threats: Exploiting Human Errors
Strange emails and website links delivered from unknown sources. These gates to the company’s confidential data exploit human errors, allowing for unauthorized access to all systems and services. The two most commonly used terms related to social engineering threats are “phishing” (access via email) and smishing (text messages). The European Parliament website informs that in Europe, the Middle East, and Africa, this method covers almost 60% of cyber security breaches. 60%! Can you imagine?!
How to avoid:
![]() Well-trained and aware personnel are important while running a business so they do not open suspicious links, messages, etc. And what’s more, they’re aware of what actually is suspicious. Let’s not forget that human errors are still one of the most common causes of data loss and system failure. You can prevent this by training your employees regularly on how to secure your data. You can also test their knowledge and skills with quizzes, simulations, or audits to make sure they are doing their jobs well.
Well-trained and aware personnel are important while running a business so they do not open suspicious links, messages, etc. And what’s more, they’re aware of what actually is suspicious. Let’s not forget that human errors are still one of the most common causes of data loss and system failure. You can prevent this by training your employees regularly on how to secure your data. You can also test their knowledge and skills with quizzes, simulations, or audits to make sure they are doing their jobs well.
Threats Against Availability: Denial of Service
Aiming to disrupt or degrade the performance of a system or service by overwhelming it with excessive traffic or requests is more prevalent among cyber threats. These kinds of attacks affect the availability, reliability, and quality of the system or service, causing delays and data losses. Open-E JovianDSS is a remarkable software for data storage infrastructure and backup management. However, you would still need a 3rd party software to protect your business systems from threats to their availability.
How to avoid:
![]() Filtering involves blocking or dropping malicious packets or requests based on their source address, destination address, port number, protocol type, or content. Filtering can be done at different levels of the network, such as routers, firewalls, or load balancers.
Filtering involves blocking or dropping malicious packets or requests based on their source address, destination address, port number, protocol type, or content. Filtering can be done at different levels of the network, such as routers, firewalls, or load balancers.
![]() Limiting the rate of packets or requests sent or received by a source, destination, or service in a given time interval. Rate limiting can reduce the impact of excessive traffic and prevent resource exhaustion.
Limiting the rate of packets or requests sent or received by a source, destination, or service in a given time interval. Rate limiting can reduce the impact of excessive traffic and prevent resource exhaustion.
![]() Redundancy as the process of increasing the capacity and availability of a system or service by adding more servers, networks, or paths. Redundancy can help distribute the load and improve the resilience of the system or service against failures or attacks.
Redundancy as the process of increasing the capacity and availability of a system or service by adding more servers, networks, or paths. Redundancy can help distribute the load and improve the resilience of the system or service against failures or attacks.
Supply-Chain Attacks: Targeting The Relationship Between Organizations and Suppliers
It combines two kinds of attacks – on the supplier and on the customer. Increasing system complexity and hardware requirements force business owners to compromise between safety and compatibility. Very often, the company must choose a less safe system that works smoothly with the hardware this company owns. It cannot lead to anything good.
How to avoid:
![]() Using a hardware-agnostic data storage system that relieves you from having to choose between software selected by the hardware you have or buying new hardware, allowing you to use the best software on the market.
Using a hardware-agnostic data storage system that relieves you from having to choose between software selected by the hardware you have or buying new hardware, allowing you to use the best software on the market.
Using the Opportunity
Working in a digitized business makes us all aware of how important cybersecurity is. Companies and governments across the world have spent millions of dollars to develop security and be cyber-proof against cyberattacks. Why? There is one reason.
Hackers are clever and daring enough to find new methods of illegal access to confidential data. But there is one important thing that makes us a bit more secure in everyday life – awareness.
That’s why there is one particular month acclaimed as a Cybersecurity Month. Multiple organizations (government and non-profit) organize hundreds of activities people can take part in to be more aware, experienced, and better trained. Specialists across the world share their experiences and novelties regarding security and stability in cyberspace. Unfortunately, this is not a battle we can win by crushing the enemy – hackers. But in October, we can all learn more about what we can do to be less vulnerable and more able to defend ourselves. Let’s use this opportunity.





Leave a Comment