Main Open-E JovianDSS Features for iSCSI Data Storage Solutions
iSCSI, the Internet Small Computer Systems Interface protocol, is a block-based set of commands that connects computing devices to networked storage. iSCSI transports data between the iSCSI initiator and the storage target over TCP/IP (Ethernet) networks.
Thanks to the simplicity of the configuration and the possibility of using the Ethernet network, the iSCSI protocol is an ideal choice for SMB companies as well as budget server setups. The main advantage of iSCSI is the ability to create an iSCSI SAN through the extensive use of typical networking elements which in turn facilitates system building and reduces its costs.
Benefits of Using Open?E’s
iSCSI Data Storage Solutions
VMware-Ready Storage Solution
Open-E software is certified with it’s iSCSI drivers by VMware to meet the most demanding requirements of virtualization. Create hundreds of virtual machines on your Open-E iSCSI data storage solution with no risk of affecting performance or data loss.
Flexible Configuration
iSCSI LUNs (LUN is a logical unit number that identifies a configured set of disks that is used as a single logical data storage unit) that can be attached to any system in the network. This allows an administrator to design the setup to optimize system performance and usability. Open-E software simplifies this configuration process even more by using the iSCSI initiator to allow other iSCSI sources to be attached to the system and you can even grow the volume space of iSCSI volumes without the need to switch off the system.
Excellent Performance for a Reasonable Price
In comparison to Fibre Channel, Ethernet networks are less expensive and can reach a level of performance that is high enough to suit most customers’ requirements. iSCSI uses standard Ethernet switches and can run different Ethernet speeds (1, 10, and 40GbE). The performance can be further improved with multi-pathing and tuning tools that adapt to different scenarios. Open-E software is a great option when it comes to high availability storage for a reasonable investment, especially for SMBs.
Hardware Independence
Build your storage system with hardware components that suit your needs and requirements. There’s no need to be stuck with a certain vendor or to cope with capacity limitations. You can easily expand your storage space as your data grows and adapt your storage to control your total cost of ownership.
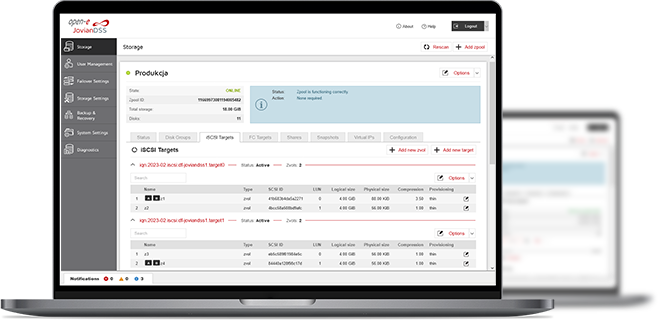
Easy to Use Software
Open-E’s data storage software is easy to install and provides simplified maintenance of iSCSI SANs via the WebGUI. No special training is required, as storage administrators already use common TCP/IP network protocols. The iSCSI session manager makes storage management a simple task by displaying current connections to iSCSI targets with all the necessary details i.e. target name, IP address, CID (connection ID), etc. The entire configuration can be done solely in the WebGUI and there is no need to use complicated command lines.
Data Storage Security
To ensure data storage security, Open-E’s software provides security tools for iSCSI such as a Challenge Handshake Authentication Protocol (CHAP) and an Internet Protocol Security (IPsec) network protocol suite for secure connections. Also, snapshots are a great addition to your backup plan as they allow you to restore deleted files or recover them after a virus attack.

Check Open-E JovianDSS and Embrace Next-Gen Data Storage!
Unlock superior performance, reliability, and future-ready scalability with Open-E JovianDSS. Ensure your data storage technology meets the demands of tomorrow.
Learn more about Open-E JovianDSSWant to Learn More?
3-in-1 Complete Data Storage Solution
Accelerate Your Data Storage with ZFS-based Storage System

Find the Exact License for Your Storage Setup
This calculator helps you to find the exact license required for your storage setup with Open-E JovianDSS, based on your individual specification.
Enter the configuration of your choice into the calculator and generate a PDF report.
Open-E Library





