All You Need to Build Your Business Continuity & Disaster Recovery Plans for the IT Infrastructure
Continuous availability of all data keeps the business going and allows you to maintain all operations even should a critical situation or disaster happen. This can be achieved by combining High Availability Clusters with Open-E JovianDSS On- & Off-Site Data Protection for maximum security. Both the features are built into Open-E JovianDSS’ core functionality suite and don’t cost anything extra.
Open-E JovianDSS Business Continuity solutions help you to be prepared for every disruption that could occur so that you can operate uninterrupted or with the lowest possible downtime during scheduled events such as maintenance tasks.
Open‑E JovianDSS Data Self-Healing and Scrubbing Features

One of the fundamental Business Continuity challenges is to sustain your data integrity and availability, while also protecting it against things like silent data corruption that can occur on every physical drive. With ZFS-based data-healing functionality, you can easily prevent silent data corruption without human intervention. The system will detect and fix the damage itself during regular read operations. You can also run the Scrub operation manually, which will scan your data storage for you and fix any corrupted data thus ensuring that less frequently used data isn’t lost.
Open‑E JovianDSS High Availability Clusters
High Availability architecture provides you with data storage that has the highest possible performance, reliability, availability, redundancy, and efficiency. By ensuring that these standards are as high as possible, downtime periods are minimized and single points of failure are eliminated. High Availability Clusters ensure business continuity by providing uninterrupted access to data during hardware failures, planned maintenance tasks, and system updates.
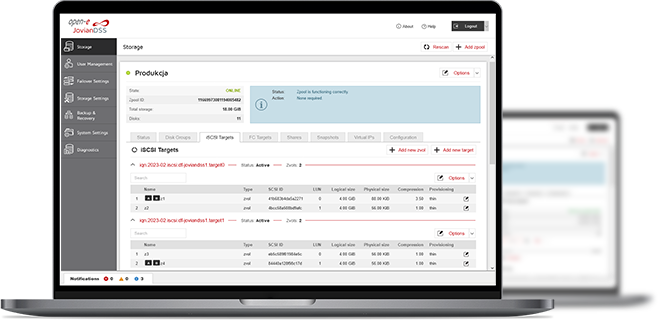
Open-E JovianDSS offers dozens of options in regards to setting up High Availability environments with iSCSI, Fibre Channel (FC) and NFS, SMB (CIFS) client protocols. These options allow you to set up High Availability Load-Balanced Storage Clusters that ensure reliability and redundancy through failover in case of a server crash.
Support for Various Cluster Environments
Ranging from small cluster-in-a-box setups to big rack servers with multiple JBODs.
All Major File- and Block-based Protocols
Open-E JovianDSS supports iSCSI, Fibre Channel (FC) and NFS, SMB (CIFS) client protocols.
Hyper-converged Clusters
Possibility to configure clusters with physical servers as well as with virtual appliances, especially in hyper-converged environments.
Distances between 1 foot to 50 miles
Range of possible distances between the nodes from local sites to stretched metro storage clusters.
Easy Cluster Management
Easy cluster configuration and management with intuitive GUI. Automation of configuration is possible via REST API's.
Flexible Cluster Over Ethernet
With dual storage mirrored over Ethernet (only with the Advanced Metro HA Cluster Feature Pack).
Open‑E JovianDSS Failover Options
Should one of the data storage nodes fail, or you just plan to reboot the system, the failover function will redirect the data flow from the unavailable server to the available one.
Active-Passive Failover Data Storage Setup

The Active-Passive setup allows you to have all your active volumes on one server (the primary node) while the other server has all the passive copies and can take over the tasks in case of an emergency (the passive node).
Active-Active Failover Data Storage Setup

A load-balanced Active-Active Failover doesn’t have a primary or secondary node. It adds extra performance by enabling the user to decide which volumes are active on which node. The failover process is the same, but the servers are able to utilize their full network performance and eliminate the unnecessary cost of idle hardware.
Normal Mode vs Disaster Mode

High Availability Architecture Examples
Open-E JovianDSS helps you build your storage environment flexibly and according to your individual business’ needs. Whether you need a system based on two nodes, multiple JBODs over SAS/FC, or even with two servers and a common set of direct-attached hard drives within one server enclosure, Open-E JovianDSS can offer you a plethora of options to architect your storage environment.
Cluster-in-a-Box
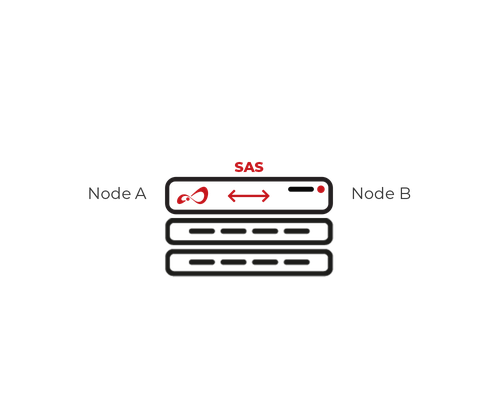
Compact, high-performance computing system with multiple servers in one enclosure.
Common Storage Cluster over SAS
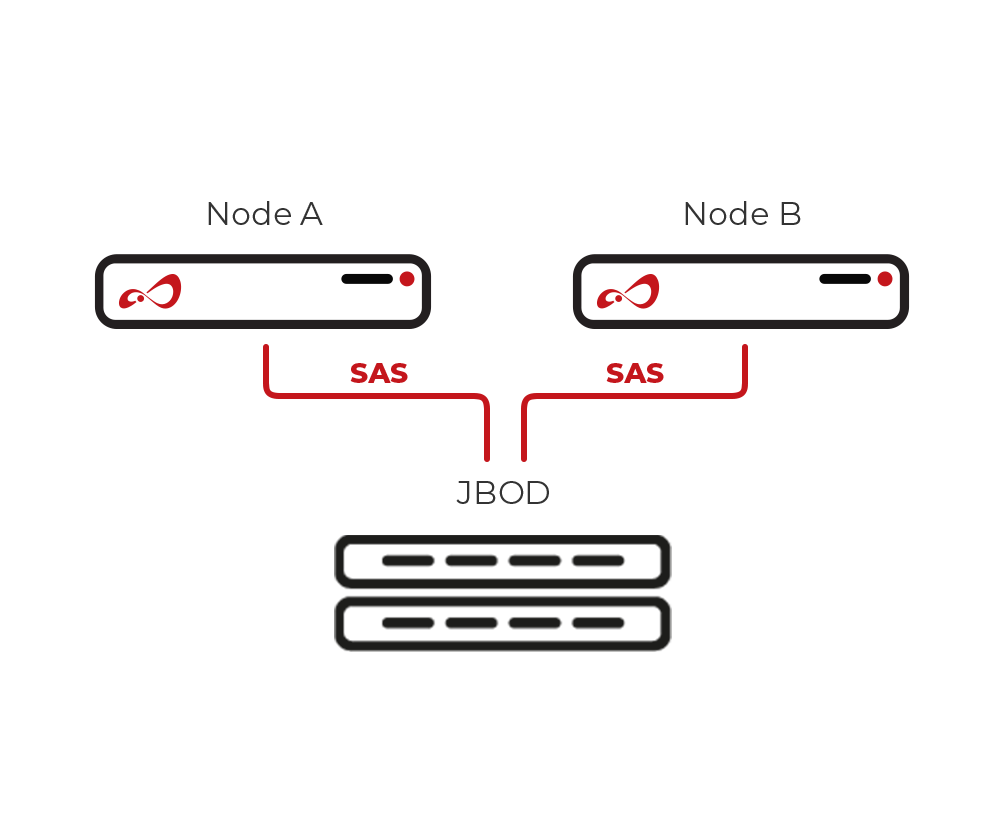 Common Storage Cluster over SAS provides shared storage solutions, enhancing data accessibility and scalability for diverse computing environments.
Common Storage Cluster over SAS provides shared storage solutions, enhancing data accessibility and scalability for diverse computing environments.
Cluster with multiple JBODs over SAS or FC
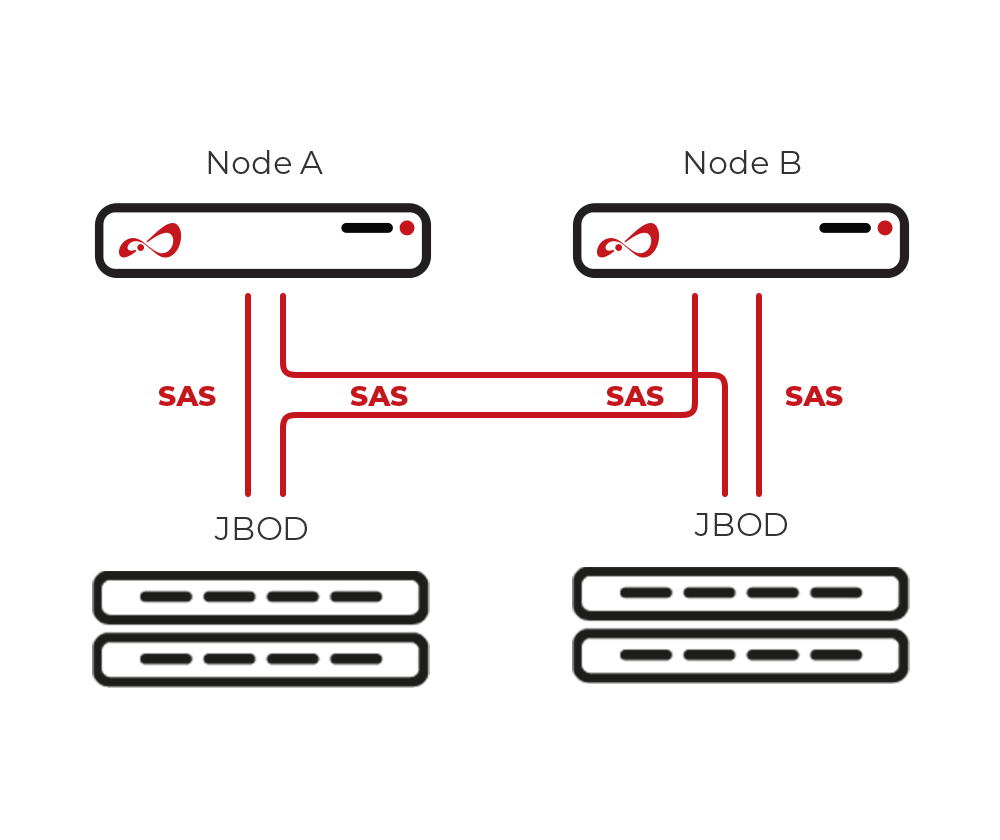 Cluster with multiple JBODs over SAS/FC offers scalable storage solutions, enhancing data management and accessibility for high-performance computing environments.
Cluster with multiple JBODs over SAS/FC offers scalable storage solutions, enhancing data management and accessibility for high-performance computing environments.
Cluster over Ethernet
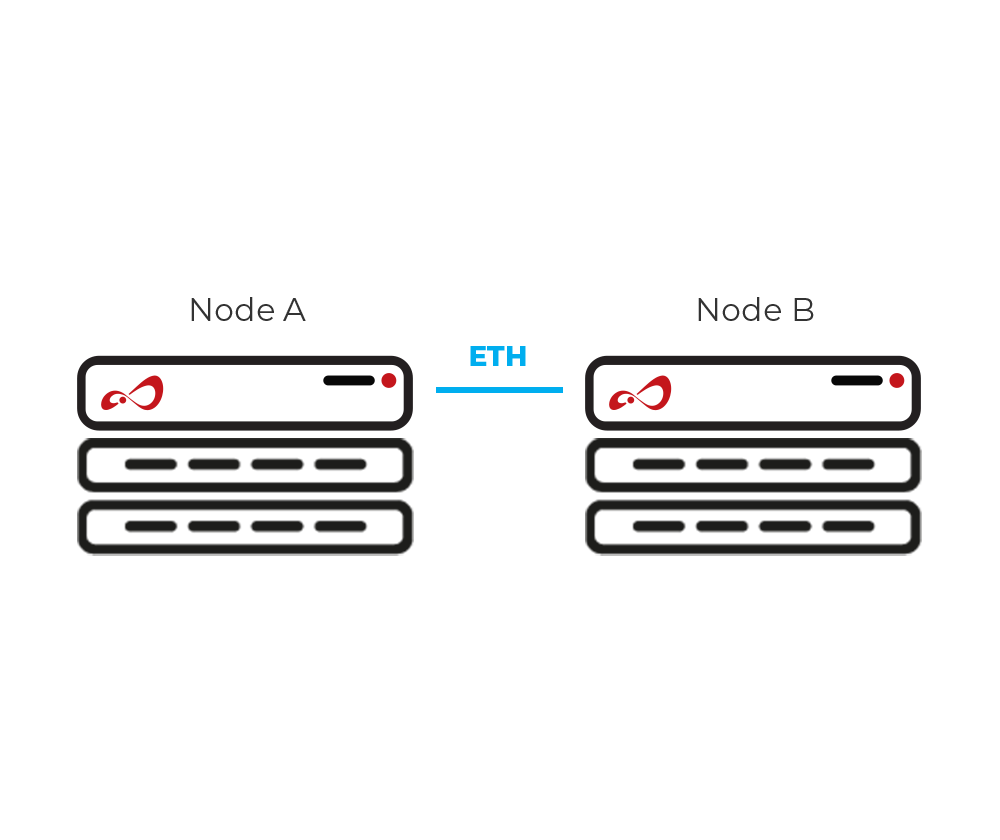 Ethernet-based cluster for efficient computing.
Ethernet-based cluster for efficient computing.
Cluster with Multiple JBODs Over SAS/FC with ATTO Bridges
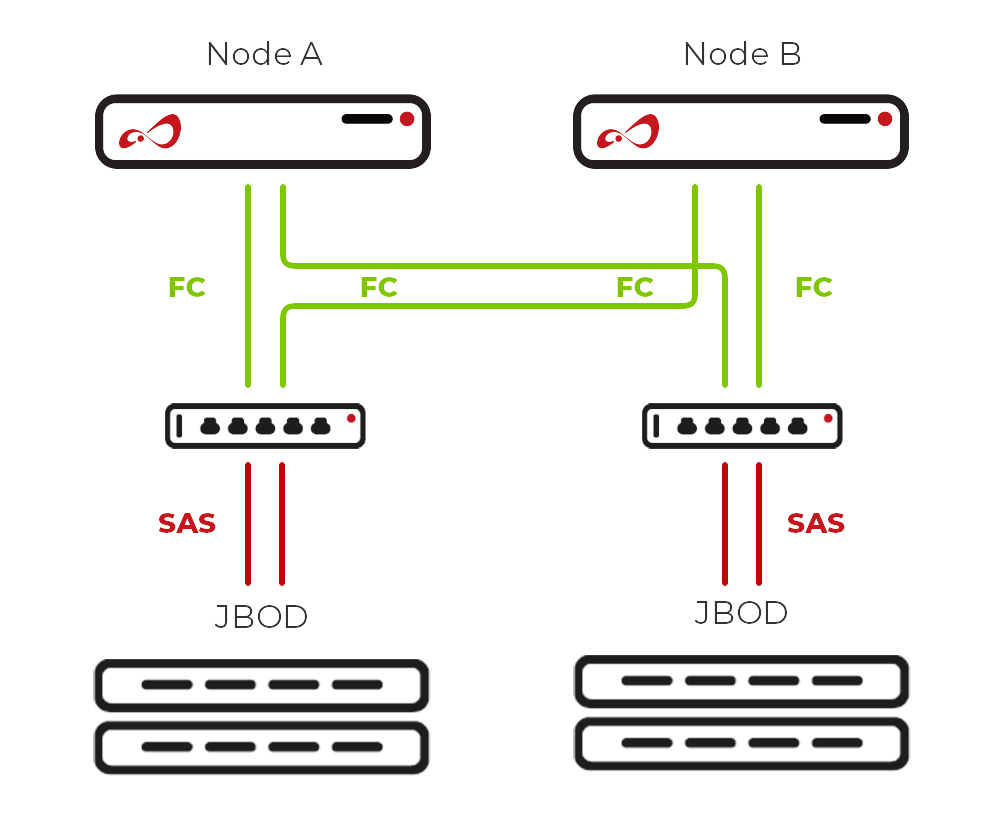 Cluster with multiple JBODs over SAS/FC utilizing ATTO bridges for enhanced connectivity and storage scalability.
Cluster with multiple JBODs over SAS/FC utilizing ATTO bridges for enhanced connectivity and storage scalability.
Cluster over SAS with Internal SAS Eexpander
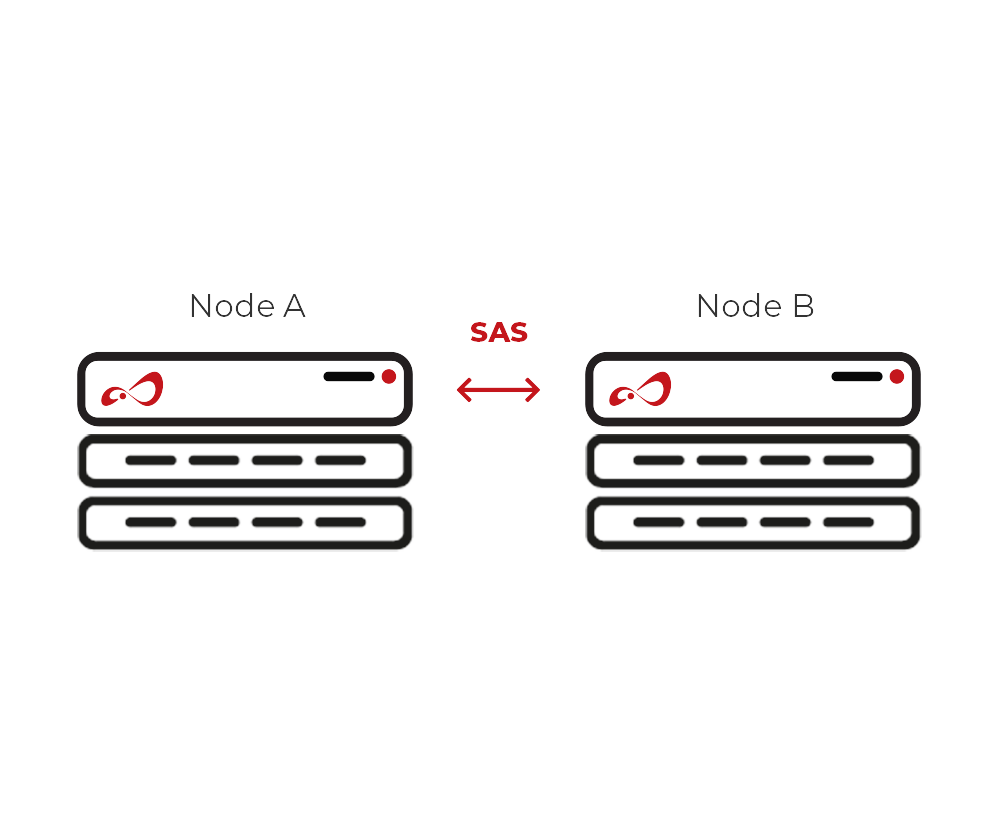 Cluster over SAS with internal SAS expander enables high-speed, scalable storage solutions for enhanced data processing and management.
Cluster over SAS with internal SAS expander enables high-speed, scalable storage solutions for enhanced data processing and management.
Open‑E JovianDSS On- & Off-Site Data Protection for Disaster Recovery
Open-E JovianDSS On- & Off-Site Data Protection is your insurance policy in the event of unexpected, data-affecting situations. As such, it should be an obligatory part of your Disaster Recovery Plan, along with the resources and procedures to instantly restore the data. It protects your data by constantly backing it up and storing copies both locally and remotely, which, in turn, allows you to restore the data to a previously saved point-in-time in case of any unexpected events.
Open‑E JovianDSS Disaster Recovery Features
Open-E JovianDSS On- & Off-Site Data Protection gives you the following possibilities of disaster recovery should data loss occur:
Instant Data Restoration from the Same Server
Crucial or "hot" data can be restored instantly from one of the multiple snapshots through the Snapshot Rollback function. Users can also access the snapshot data and manually restore any and all selected files. This can be helpful should a ransomware attack occur since snapshots are read-only files, thus they can be used to restore the data even if the rest of the data on the server is encrypted.
Restoring Data from a Local Backup Server
With a local backup server, data is available in the same location and can be recovered with a minimum amount of downtime by temporarily using a backup server as the data server while the primary server is being restored. This approach protects you against data loss due to hardware failure.
Restoring Data from Off-Site Locations
It is possible to instantly switch to the backup server and use it temporarily as a primary location (depending on the system structure) while doing the restore in the background. Restoring data from an off-site server may be more time-consuming, depending on the amount of data that needs to be recovered, as well as the connection throughput. That being said, it’s also one of the only ways to protect data against natural disasters such as floods, fires etc, as well as man-made ones like power shortages or thefts.
Open-E JovianDSS
- Other Features
Data Storage Software
Ensure your data integrity, reliability and safety with all-in-one data storage software.
Backup Solution
Keep your data secure with the built-in, comprehensive backup solution.
Want to Learn More?
3-in-1 Complete Data Storage Solution
Accelerate Your Data Storage with ZFS-based Storage System

Find the Exact License for Your Storage Setup
This calculator helps you to find the exact license required for your storage setup with Open-E JovianDSS, based on your individual specification.
Enter the configuration of your choice into the calculator and generate a PDF report.
Open-E Library






