An Easy Way to Centralize Your Data
NAS (Network Attached Storage) and SAN (Storage Area Network) are storage technologies that can simplify your work and improve the collaborative process in your company. NAS filers are dedicated to file sharing, while SAN provides access to consolidated, block-level data storage – both deliver the necessary capabilities for storing and sharing data.
Centralization reduces the costs of storing data in various locations, increases the efficiency of disk usage, and provides a central repository for all your documents. SAN and NAS servers are optimized to store and send even terabytes of data to multiple devices simultaneously. Your data can be accessed remotely as long as there’s a connection to the network.
Centralization of data also makes the backup process much easier. To ensure the security of your data, Open-E Data Storage software handles user access control and permission assignments so your employees only access the resources you want them to.
SAN vs NAS Usage Comparison

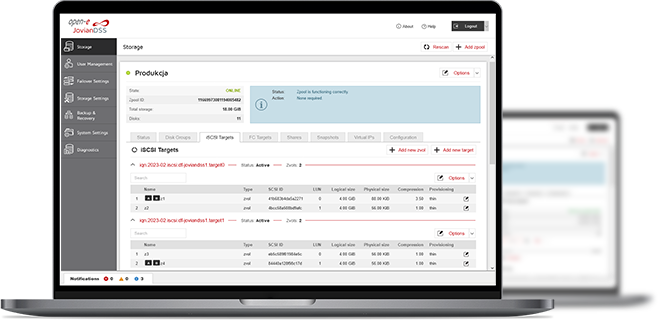
Check Open-E JovianDSS and Embrace Next-Gen Data Storage!
Unlock superior performance, reliability, and future-ready scalability with Open-E JovianDSS. Ensure your data storage technology meets the demands of tomorrow.
Learn more about Open-E JovianDSSCentralizing All Data to a Single System
- Download & Read The Brochure

File size: 28.3 MB
Discover the benefits of centralized data storage infrastructure with our detailed guide! The brochure offers an extensive overview of the advantages and implementation strategies for centralized data storage, addressing key elements to assist you in modernizing your data management processes with Open-E JovianDSS. Inside the brochure, you will find:
- Step-by-step Guide Explaining Centralized Data Storage Infrastructure Substance
- Types of Centralized Data Storage Systems
- Implementing Centralized Data Storage
- Management and Maintenance of Centralized Data Storage
- Forward-thinking Approaches in Centralized Data Storage
- Use Cases and Examples
Want to Learn More?
3-in-1 Complete Data Storage Solution
Accelerate Your Data Storage with ZFS-based Storage System

Find the Exact License for Your Storage Setup
This calculator helps you to find the exact license required for your storage setup with Open-E JovianDSS, based on your individual specification.
Enter the configuration of your choice into the calculator and generate a PDF report.
Open-E Library






